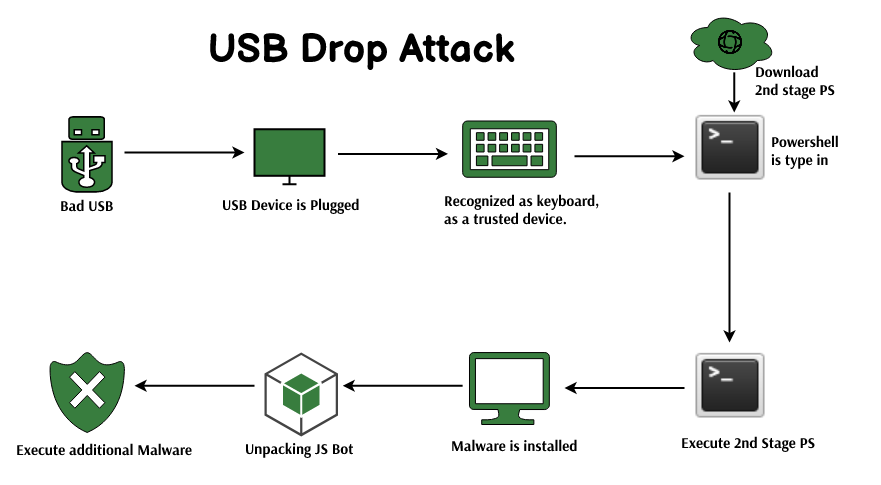
USB Malware Threat: Hackers Exploit News and Media Hosting Sites - Protergo Cyber Security | Indonesia

Amazon.com: USB Defender | Data Blocker | Blocks Unwanted Data Transfers | Protects Smartphone & Tablets From Public Charging Stations | Hack Proof, 100% Guaranteed : Electronics

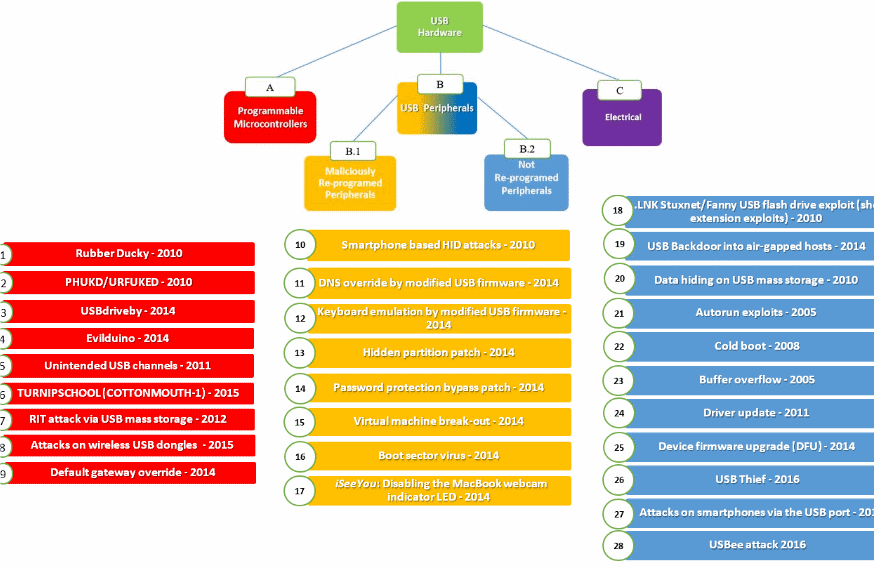
USB Device Under Threat. New Hack Is Undetectable And Unfixable – Cyber Security Experts – Middle East | Eastern Province | Al-Khobar, Kingdom of Saudi Arabia

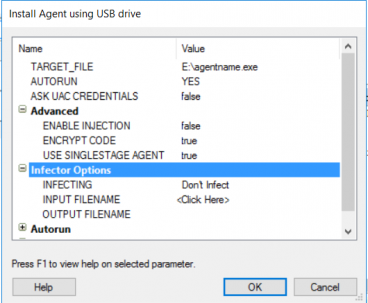
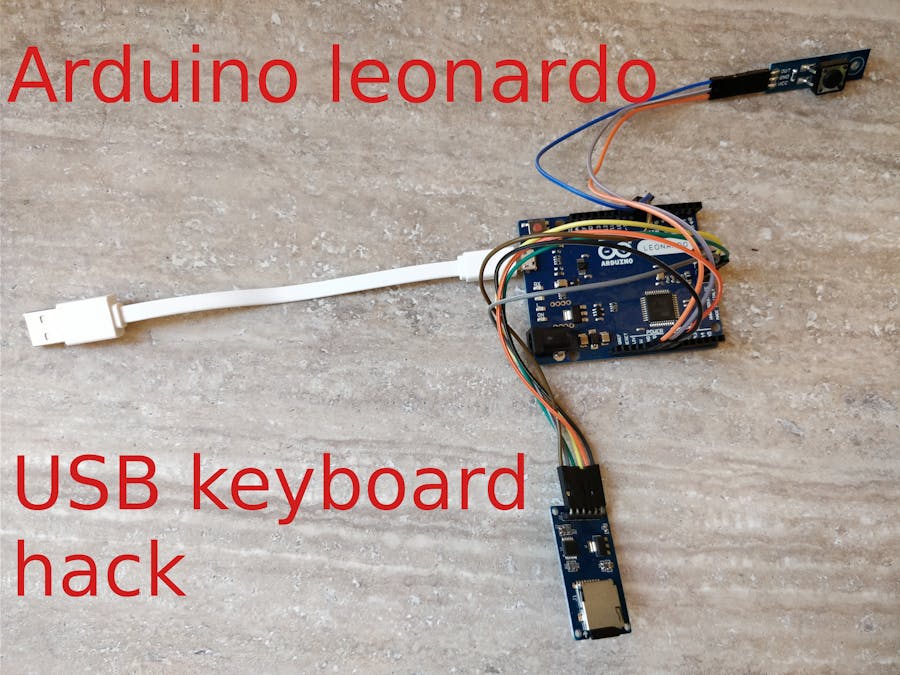
How I made a programmable hacking USB device to infiltrate PCs? | by Aditya Anand | InfoSec Write-ups











/cdn.vox-cdn.com/uploads/chorus_asset/file/18993465/omg3_800x.jpg)